Security Testing and Assurance
Seven things you should know about CORIE
The CORIE guidelines take international best practice, including the CBEST and TIBER frameworks, and applies an Australian context to ensure the guidelines are relevant and impactful.

What is CORIE?
CORIE (or Cyber Operational Resilience Intelligence-led Exercises) is a regulatory framework introduced by the Australian Council of Financial Regulators to improve cyber security resiliency in the Australian financial system. The goal of the CORIE program is to test and strengthen the cyber resilience of financial institutions against known threat actors and in so doing safeguard Australian financial markets.
Cyber risk is repeatedly classified as one of the top risks to the Australian financial system and is acknowledged as a key risk by the Council of Financial Regulators. The CORIE guidelines take international best practice, including the CBEST and TIBER frameworks, and applies an Australian context to ensure the guidelines are relevant and impactful.
Additionally, by focusing on being intelligence-led, these guidelines ensure that they can incorporate current events, industry-specific threat activity, and up to date threat intelligence to simulate realistic real-world attacks.


What does CORIE deliver and why is it important?
The CORIE guidelines are important because they provide a structured approach for adversarial attack simulation, delivering meaningful results reflective of the real-world threats facing the industry.

For the industry
CORIE provides a structured framework to work towards directing security testing efforts in a way which delivers simulations of genuine real-world attackers and helps to prepare financial services institutions to deal with these threats. Aligning to a regular program of testing which simulates an evolving threat landscape provides the industry with improved awareness and understanding of serious cyber security threats.
For the public
For financial institution customers and the everyday public, CORIE is important as a demonstrative measure taken to improve the security of Australia’s financial industry. The rise of ransomware incidents and frequent public breaches has brought cyber security firmly to the forefront of public awareness, and the CORIE exercises will provide greater confidence in the industry in an uncertain time.

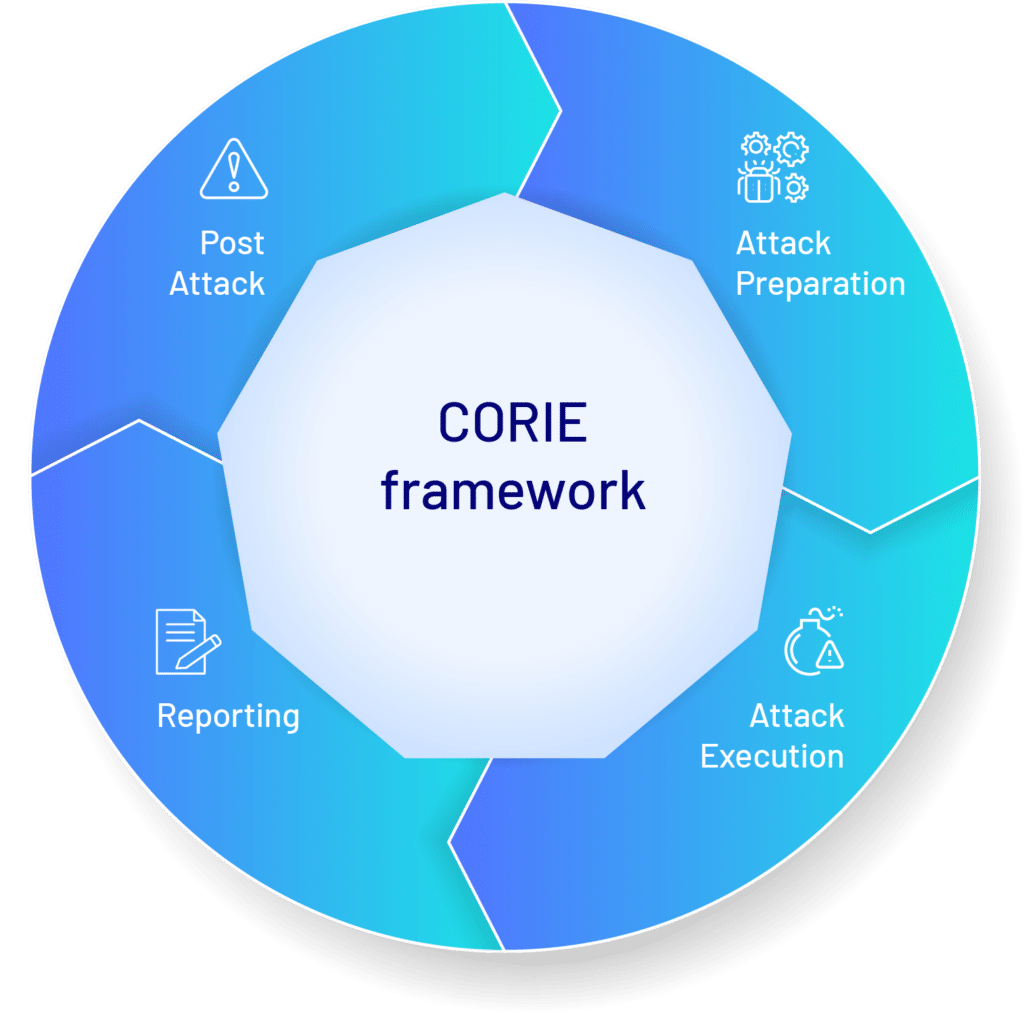
What are the elements of the CORIE Framework?
The CORIE framework outlines the activities in detail, however there are several key elements of the CORIE framework to understand.
![]()
Attack Preparation
Threat Intelligence based Scenarios
Critical to the CORIE exercises are the Threat Intelligence-based Scenarios – specific testing scenarios and attack patterns based on the tactics, techniques, and procedures (TTPs) of known threat actors. At this stage it is critical to work with up to date, industry specific and local threat intelligence to devise the best possible scenarios.

Attack Execution
Scenario based Adversary Simulation
The attack execution aspect of the CORIE framework is where most of the activity happens, with expert computer security specialists emulating the behaviour and attack patterns of threat actors as detailed in the Scenarios.
Reporting
Attack Reporting and Remediation Planning
The reporting aspect of the CORIE framework covers the process of reporting results from the Attack Execution stage and transforming these into useful, actionable guidance to improve resiliency. The CORIE exercise should provide you with a report readable and relevant to all levels of the business which replays the attacks and details outcomes of the exercises. This stage also includes reporting provided back to the Council of Financial Regulators on the exercises and their outcomes.

Post Attack
Purple and Gold Team Exercises
Gold and Purple Team exercises are critical as part of the end-to-end process of delivering CORIE exercises.
Purple Team exercises provide an opportunity to break the exercise attack chain down into key TTPs or attack flows, that provide detection opportunities. The security testing team and financial institution security team work collaboratively to identify TTPs that were used during the exercise but did not result in meaningful detections and uplift the FIs ability to detect and respond to the activity.
Gold team exercises provide financial institution leadership teams with an opportunity to test incident response practices and understand the context of the Reporting stage findings.

Where should I start?
Not all organisations will be required to conduct CORIE exercises as soon as the regulations are released, and not all organisations may be ready for the level of maturity required of these exercises.
In general, it is best to conduct a CORIE Readiness Assessment to determine if these exercises are right for your organisation. For example, it may be more appropriate to conduct a CORIE aligned Red or Purple Team exercise with a view to implement security findings from these tests in preparation for future CORIE exercises. It is also important to right size the exercise to your business and technology context, or stage in your life cycle, ensuring you get the best possible value for money. These exercises can range from an informational brief on the CORIE exercises, to a CORIE Readiness Assessment aligned to your maturity through to a full CORIE aligned engagement.
CyberCX is always pleased to provide its expertise and can help you understand these guidelines and how best to apply them to your organisation.


Who wrote the CORIE Framework?
The CORIE framework includes learnings from several existing similar schemes, including CBEST, TIBER, iCAST and AASE. It has been designed by the Council of Financial Regulators Cyber Security Working Group to establish a best practice framework specific to the Australian industry and has begun a pilot stage with a small number of financial institutions in the industry.

Tips, tricks, and pitfalls to avoid
Before
Certification/Accreditation (Preparation)
Before beginning an exercise, consider if your organisation is ready for a full CORIE exercise. If it is, then you will also want to consider what areas of your business should be included for the exercise to avoid any critical business risks (blindspots) while also allowing meaningful security testing.
It is also important to determine clear rules of engagement, lines of communication, and where required conduct activity pre-approval for the team engaged to ensure the exercises can be conducted safely and effectively.
Lastly, it is important to consider the regulatory obligations of the exercises, as a key component is the reporting delivered to the Council of Financial Regulators following the conclusion of the scenarios.
During
Certification/Accreditation
During the exercises it is important to maintain clear communication, understand which members of the team are and are not informed of the exercises, and monitor on a continual basis for risks arising from the scenarios.
After
Certification/Accreditation
Once an exercise has been concluded, it is important for the reporting to not be the final step. CORIE exercises should produce meaningful, actionable reports which can be used to uplift your security posture. As part of CyberCX engagements, we are also able to offer technical and strategic guidance to our customers to prioritise and action these recommendations where required.
It is also important to conduct Purple and Gold Team exercises following the initial exercises, as they will best allow your organisation to absorb the learnings from the scenarios.

How to take your first steps
Your first step when considering a CORIE exercise should be to consider if they are appropriate for you. You can do this yourself by reviewing the CORIE Framework, or by engaging with a qualified provider such as CyberCX who can provide expert guidance on the exercises and the best next steps for ensuring your security and continued cyber resiliency.


Ready to get started?
Find out how CyberCX can help your organisation manage risk, respond to incidents and build cyber resilience.

