
Published by Solutions and Innovations on 7 February 2023
Here at CyberCX, we spend an extensive amount of time working with and advising customers who are undertaking their organisational journey to Essential Eight compliance. We have a long history with the controls strategies as recommended by the ACSC and strongly support the Essential Eight as a way for organisations to achieve cyber security uplifts across their internet connected assets.
Advanced threat actors use specific tools, techniques and procedures to compromise public and private sector organisations. To address the threat, the Australian Cyber Security Centre (ACSC) has developed the “Strategies to Mitigate Cyber Security Incidents” – a prioritised list of mitigation strategies designed to assist organisations in protecting their systems and infrastructure. The Essential Eight are the highest priority mitigations taken from this larger strategies list, deemed as the most effective controls to prevent and respond to attackers.
The ACSC is continuously reviewing and improving the Essential Eight to ensure it is practical and achievable for organisations in materially uplifting their cyber security. In recent months, the ACSC released strategic implementation and reporting guidelines to help ensure clarity in the interpretation of controls and how to ensure appropriate validation.
In conjunction with the updated guidance, we also saw updated reporting on the adoption and effectiveness of the Essential Eight via the Commonwealth Cyber Security Posture in 2022 report. This report highlights the importance of continual effort in ensuring robust and timely deployment of Essential Eight controls across organisations within the commonwealth and matches our experience that organisations face in implementing organisation wide security changes.
We have identified five key themes across our customers which highlighted areas where we can provide more robust services to support their journey. These are:
- Dealing with end-user workstation controls which consumes significant time during implementation phases.
- Simplifying the engagement model from the beginning of Essential Eight adoption, through to implementation and maintenance over time.
- Accessible guidance and capability to support implementation execution.
- Ongoing support to ensure implemented controls and reporting functions are fit for purpose over time.
- Further assistance for customers to build internal stakeholder confidence in being assessment ready.
With these themes in hand, we set about re-imagining how we can help customers in a timelier and streamlined way. The result of this work has resulted in additional new services we have since launched to market to help our customers.
Essential Eight Managed Controls
Wide scale introduction and deployment of controls to meet the maturity level requirements can be a time consuming and costly effort. One common point of concern for customers is how to handle widescale deployment of potentially disrupting controls across their end-user workstations. To assist with this challenge, we have worked with our partners at Airlock Digital and Devicie to introduce our Essential Eight Managed Controls service.
This service brings the extensive capabilities of Airlock Digital and Devicie, along with our extensive Managed Security experience to handle the heavy lifting of end-user workstation requirements.
Our Managed Controls solution enables your organisation’s security team to focus precious time and energy on your strategic priorities, knowing that you have taken proactive measures to keep your organisation, its systems, and data, safe against this rapidly evolving cyber threat landscape.
We achieve this by addressing the following areas, as a managed capability:
Application control
Strong Patch Management
Additional Endpoint Hardening
Multifactor Authentication
Restricting Privilege
Key takeaways:
- Accelerate Essential Eight coverage for your end-user workstations.
- Ongoing management and maintenance of key controls.
- Appropriate reporting of control deployments & effectiveness.
- Evolve controls over time as you target increased maturity levels.
Essential Eight as a Service
Based on our experience, organisations general tackle Essential Eight adoption across key phases. These include embracing Essential Eight for the organisation, determining the current level of maturity across controls and developing appropriate roadmaps for implement, implementation and controls transition followed by a continuous cycle of maintenance and reporting of implemented controls.
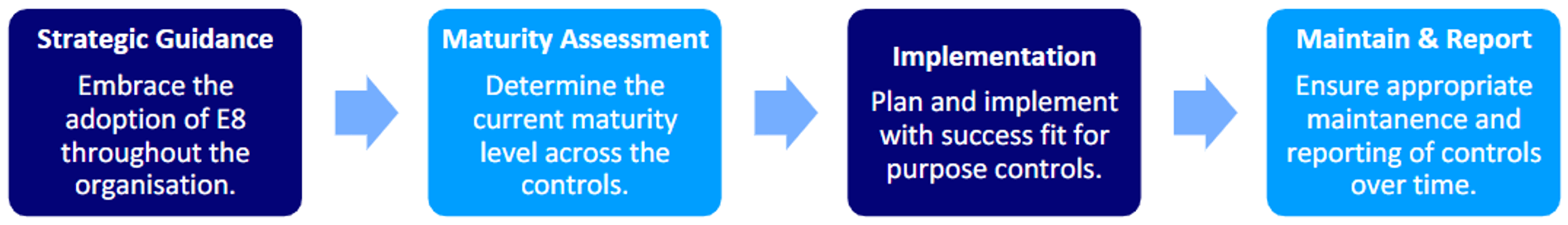
Our Essential Eight as a Service is designed to help organisations execute each phase as efficiently as possible and help with the ongoing and critical tasks relating to controls monitoring and reporting.
This begins with ensuring your wider organisation understands the Essential Eight and the benefits of adoption. We assist with stakeholder engagement and understanding of the controls, estimating the effort required for implementation and providing expert advice to help inform appropriate prioritisation decisions.
Upon completion of this initial phase, CyberCX then provides a maturity assessment which looks at your organisation, the current implementation of controls and jointly develop a roadmap for efficient and appropriate implementation for each of the eight controls.
CyberCX can then help your operational teams and systems integrators ensure successful controls deployments throughout your organisation. Critically, after successful deployment, we can help with ensuring accurate maintenance of deployed controls over time and ensure timely reporting for stakeholders
This service is backed and provided via our breadth and depth of real-world experience via 1000’s of hours of helping customers meet Essential Eight expectations.
Our purpose is to secure our communities, and we firmly believe the Essential Eight are a robust set of controls that provides material uplift to organisations cyber security posture. In providing these fresh capabilities to organisations we hope to streamline the effort required for successful Essential Eight implementation.
Essential Eight Guidance
Underpinning the above services is our experience in Essential Eight consulting. We have helped customers achieve Essential Eight maturity across a range of levels in a range of environments. This work includes (but is not limited to) the following:
- Incorporation of the Essential Eight into the wider organisations’ security strategy.
- Benefits analysis of adoption the Essential Eight for organisations.
- Stakeholder guidance, education and enablement for Essential Eight adoption.
- Baseline assessments & maturity level guidance.
- Roadmap development and implementation strategies for Essential Eight deployment.
- Process and policy development to support Essential Eight.
- Supporting documentation.
- Bespoke controls development and implementation.
Whether you are thinking about adopting the Essential Eight within your organisation, or have already started the journey, we would love to talk to you about how we can help.







